Microsoft accuses Iran's government of cyber operation against Charlie Hebdo
Microsoft’s Digital Threat Analysis Center says a hacking group within the Iranian government is behind a cyber operation that targeted French satirical magazine Charlie Hebdo.
The group — which Microsoft calls Neptunium and the U.S. Justice Department calls Emennet Pasargad — claimed in January it had stolen the personal information of 200,000 Charlie Hebdo customers after hacking into one of the magazine’s databases.
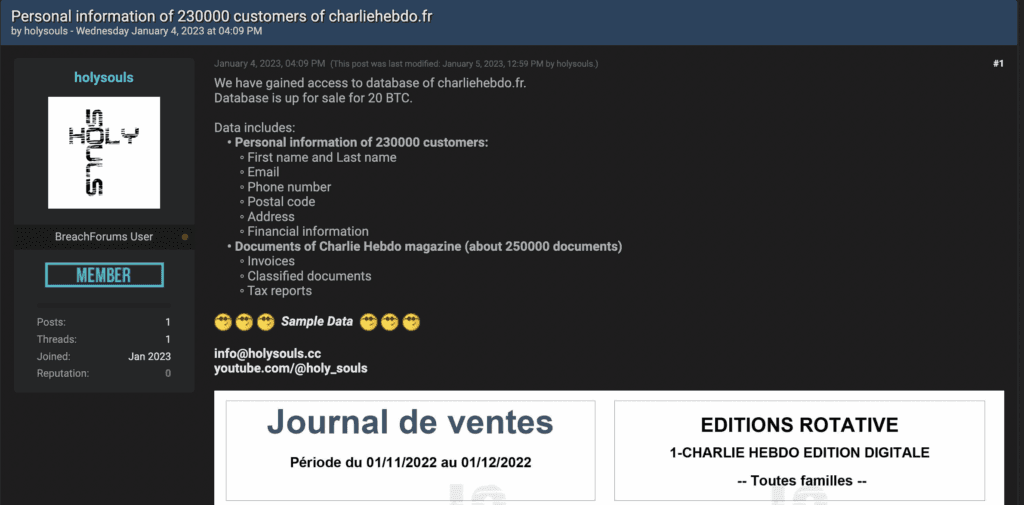
In several social media posts under the name Holy Souls, the group marketed samples of the stolen data that included names, phone numbers, addresses, emails and more from subscribers to the magazine. Holy Souls published the stolen data on YouTube and on several hacker forums, amplifying the posts across several social media platforms.
According to Microsoft, the attack was orchestrated in response to the magazine’s decision to hold a cartoon contest asking readers to submit drawings ridiculing Iranian Supreme Leader Ali Khamenei.
“The issue featuring the winning cartoons was to be published in early January, timed to coincide with the eighth anniversary of an attack by two al-Qa’ida in the Arabian Peninsula (AQAP)-inspired assailants on the magazine’s offices,” Microsoft said Friday.
“Holy Souls advertised the cache of data for sale for 20 BTC (equal to roughly $340,000 at the time). The release of the full cache of stolen data – assuming the hackers actually have the data they claim to possess – would essentially constitute the mass doxing of the readership of a publication that has already been subject to extremist threats (2020) and deadly terror attacks (2015).”
Iranian Foreign Minister Hossein Amir-Abdollahian criticized the contest as well, calling it an “insulting and discourteous action ... against the religious and political-spiritual authority.” He added that it would not be “left without a response.”
اقدام توهین آمیز و خارج از نزاکت نشریه ای فرانسوی در انتشار کاریکاتور علیه مرجعیت دینی و سیاسی بدون پاسخ قاطع و موثر نخواهد بود. به دولت فرانسه اجازه نمیدهیم پا را از گلیم خود فراتر گذارد.آنها قطعا مسیر اشتباهی را انتخاب کرده اند. پیشتر این نشریه را در فهرست تحریمها قرار دادیم.
— H.Amirabdollahian امیرعبداللهیان (@Amirabdolahian) January 4, 2023
Iran’s Foreign Ministry also demanded a meeting with the French ambassador and closed the French Institute for Research in Iran.
French news outlet Le Monde confirmed that the data stolen from the magazine was authentic.
Microsoft said it determined the attack was linked to Iran’s government because it aligned with attributes seen in several other attacks by the state, including the use of hacktivist personas taking credit for an attack, the leaking of private data, and more.
“The campaign targeting Charlie Hebdo made use of dozens of French-language sockpuppet accounts to amplify the campaign and distribute antagonistic messaging. On January 4, the accounts, many of which have low follower and following counts and were recently created, began posting criticisms of the Khamenei cartoons on Twitter,” the researchers said.
“Crucially, before there had been any substantial reporting on the purported cyberattack, these accounts posted identical screenshots of a defaced website that included the French-language message: ‘Charlie Hebdo a été piraté’ (“Charlie Hebdo was hacked”).”
Two fake social media accounts purporting to belong to a French technology executive and a Charlie Hebdo editor began posting the screenshots as well before they were suspended.
The same accounts were then used to lampoon France, joking that the “next subject of Charlie’s cartoons should be French cybersecurity experts.”
Charlie Hebdo is well known for its attempts to cause controversy through sometimes purposely-offensive cartoons and messaging. Microsoft said regardless of one’s opinions on the magazine, the leak of personal information “constitutes a grave threat.”
“Microsoft invests in tracking and sharing information on nation-state influence operations so that customers and democracies around the world can protect themselves from attacks like the one against Charlie Hebdo,” the researchers said. “We will continue to release intelligence like this when we see similar operations from government and criminal groups around the world.”
Data leakers
In October, the FBI warned of hack-and-leak operations targeting organizations in the U.S. and Israel by Emennet Pasargad, which U.S. law enforcement agencies have previously spotlighted for its role in efforts to interfere with the 2020 U.S. presidential election.
The FBI said the group — which has changed its name several time to avoid sanctions — has targeted entities in Israel since 2020 with attacks that involved the theft and leak of stolen data. They would then amplify the stolen data on social media and online forums.
“To avoid attribution, Emennet executed false-flag campaigns under the guise of multiple personas like hacktivist or cyber-criminal groups,” the FBI claimed.
The goal of the attacks is allegedly to “undermine public confidence in the security of the victim’s network and data” while other incidents are meant to embarrass companies or countries.
Emennet has also been seen using the notorious Log4j vulnerability in attacks on at least one U.S.-based organization.
In February 2022, the State Department announced a $10 million reward for information about Seyyed Mohammad Hosein Musa Kazemi and Sajjad Kashian — two Iranian contractors who worked for Emennet Pasargad and launched several operations designed to “sow discord and undermine voters’ faith in the U.S. electoral process.”
Kazemi and Kashian are still at large, believed to be located in Iran. The two were also added to the FBI’s cyber most wanted list.
The Department of Justice charged both men for their alleged role in a variety of attacks and scams. The two are accused of hacking the voter websites of 11 states. They also used spoofed accounts from far-right hate group Proud Boys to contact Republican party members with fake videos of Democratic election fraud and sent threatening emails to Democratic voters in support of former President Donald Trump.
The Justice Department said the two also hacked a U.S. media company in the fall of 2020 and sought to leverage their access on November 4, right after the election.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.



