Bitdefender, Europol, Swiss police publish decryptor for LockerGoga ransomware
Cybersecurity firm Bitdefender published a new decryptor on Friday for LockerGoga, a strain of ransomware best known for its 2019 attack on Norwegian aluminum giant Norsk Hydro.
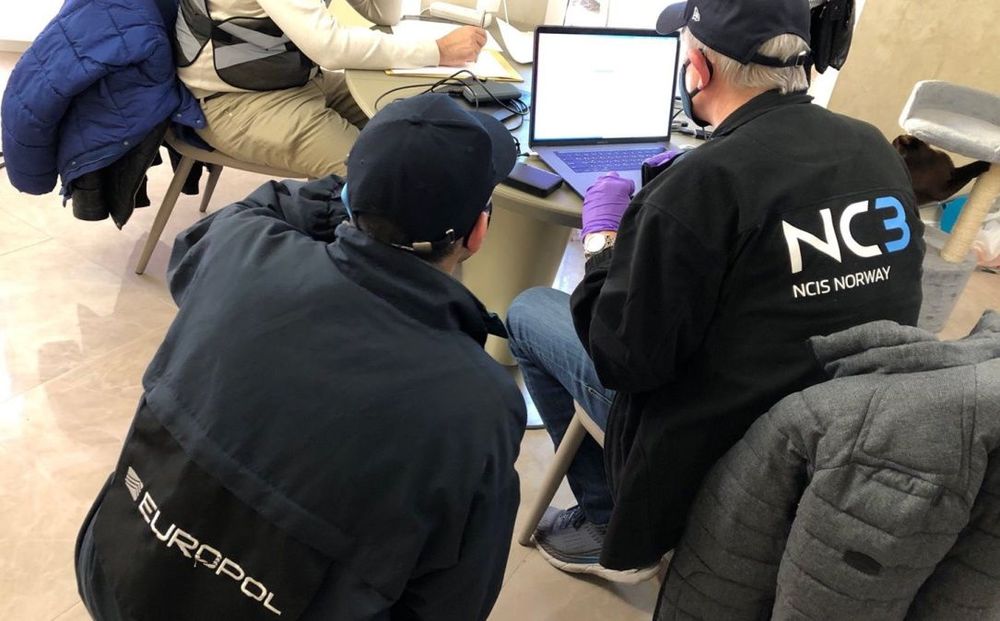
Bitdefender said it created the decryptor with the help of Europol, the Zürich Public Prosecutor's Office, the Zürich Cantonal Police and the NoMoreRansom Project.
The group behind the ransomware has not been active since October 2021, when Europol worked with law enforcement agencies from Norway, France, Netherlands, Ukraine, the U.K., Germany, Switzerland and the U.S. to arrest 12 alleged members.
The Zürich Public Prosecutor's Office said on Friday that police have spent months examining the data collected during the October 2021 raid and discovered the private keys that will unlock data from several ransomware attacks.
The group is also accused of being behind other ransomware strains like MegaCortex and Dharma. Swiss prosecutors said a decryptor for victims of MegaCortex will be released in the coming months.
“The perpetrators are accused of being involved in ransomware attacks on over 1,800 people and institutions in 71 countries,” the Zürich Public Prosecutor's Office said in a statement, noting that the decryption keys came from one specific actor who is currently being held in Zürich and is facing a range of hacking and money laundering charges.
Alongside partner organizations, the prosecutors used the master decryption key to create a universal decryptor. It is available on several websites and can scan systems before automatically decrypting any locked files.
Officials also urged those affected by the ransomware to file criminal complaints if they have not done so already.
Bitdefender Releases Universal LockerGoga Decryptor in Cooperation with Law Enforcement: https://t.co/nkeXV9xv88
— BitdefenderLabs (@BitdefenderLabs) September 16, 2022
Bitdefender told The Record that the universal decryptor is free and will help victims recover encrypted data from all past LockerGoga ransomware attacks. LockerGoga ransomware allegedly caused an estimated $104 million in damages, according to Bogdan Botezatu, director of threat research and reporting at Bitdefender.
Botezatu said the lack of activity from LockerGoga over the last year shows that the raid was successful.
“LockerGoga debuted in January 2019 with quite a splash — a series of significant infections against large industrial companies in the United States, France and other countries,” he told The Record.
For example, the ransomware was implicated in attacks on French engineering consulting firm Altran, as well as manufacturing companies Hexion and Momentive.
“Looking at the entities known to have suffered LockerGoga infections, the victimology is large companies in the industrial and manufacturing sector,” he said.
Recorded Future ransomware expert Allan Liska said LockerGoga was an “old school” group that did not have an extortion site or use the ransomware-as-a-service model, whereby affiliates pay to use a ransomware strain.
Many experts considered the gang a “third tier” ransomware group because although they did have some large-scale attacks, they “didn’t have the force multiplier of a RaaS offering.”
“They were based out of Romania, and I believe all the members of their criminal group resided in country,” he said.
“A decryptor released now likely only helps victims who did not pay and left impacted systems offline and untouched since they were attacked.”
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.