Billion-dollar rail firm confirms data breach after suspected ransomware attack
One of the world’s largest rail and locomotive companies announced a data breach this week that involved troves of employee information following an alleged ransomware attack last summer.
Wabtec, which has about 25,000 employees and operates in 50 countries, began sending out breach notification letters on December 30 letting people know that data was stolen from their systems during a cyberattack they discovered last June.
In a statement, the company said it contacted the FBI and hired a cybersecurity firm, which discovered that the hackers “introduced malware” to certain systems as early as March 15.
The investigation found that systems containing sensitive information were accessed and data was exfiltrated before being posted to a leak site. Wabtec confirmed the findings on November 23 and began sending out breach notification letters on December 30.
The company did not respond to requests for comment about how many people were affected by the incident but in their release it confirmed the leaked information included names, dates of birth, passport numbers, USCIS or Alien Registration Numbers, National Health Service Numbers for people in the United Kingdom, health insurance information, Social Security Numbers, financial account information, data on criminal convictions, as well as on sexual orientation, and more.
Unlike in many data breach incidents, Wabtec is not offering any free credit monitoring and identity theft protections to the people affected. The company urged victims to simply “remain vigilant against incidents of identity theft and fraud by reviewing their financial account statements and credit reports for any anomalies.”
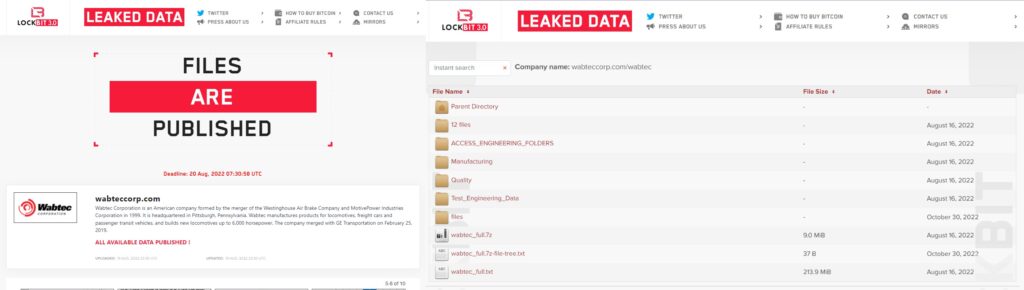
While Wabtec would not confirm whether the incident involved ransomware, the LockBit ransomware group posted data stolen from the company in July and eventually leaked all of the data in August.
Credit: Ron Fabela
Ron Fabela, co-founder of industrial cybersecurity firm SynSaber, told The Record that what stood out to him about the breach notification is the length of time since when the data was published.
“This lag in breach reporting is not uncommon and continues to be a focus for industry and government policy makers,” he said.
The Transportation Security Administration (TSA) unveiled new cybersecurity regulations for passenger and freight railroad carriers in October, mandating that companies develop network segmentation policies and controls that separate operational technology systems from other IT systems in case of compromise.
Fabela noted that the attack seemed to only target the company’s human resources systems and not any of their industrial control systems or plant operations.
“While industrial processes are not the intended target, widespread IT outages can have a splash damage effect on processes,” he said.
“Ransomware continues to be a challenge for organizations, with the Wabtec breach being no different. This attack appears to be a straightforward double-extortion attack with the sensitive files published back in August 2022.”
Experts noted that as the rail industry continues to become more automated, cyber risks have increased – making the potential consequences of a cyber event “damaging and deadly.”
The rail industry has seen its fair share of cyberattacks in recent years. In April 2021, the New York City’s Metropolitan Transportation Authority – one of the largest transportation systems in the world – was hacked by a group based in China.
While the attack did not cause any damage and no riders were put at risk, city officials raised alarms in a report because the attackers could have reached critical systems and may have left backdoors in the system.
The same month, the Santa Clarita Valley Transportation Authority was hit with a ransomware attack, and in 2020, the Southeastern Pennsylvania Transportation Authority was also hit with ransomware.
Last year, Homeland Security Secretary Alejandro Mayorkas announced new cybersecurity regulations for U.S. railroad operators requiring them to disclose any hacks, create cyberattack recovery programs and name a chief cyber official. Those regulations expired in December.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.



