Atlassian warns of several new critical vulnerabilities potentially being exploited in wild
Atlassian is warning its customers and partners about three different critical vulnerabilities affecting Confluence Server, Confluence Data Center as well as several other products from Bamboo, BitBucket, Fisheye and Jira.
On Thursday, Atlassian warned that CVE-2022-26138 – which affects the Questions For Confluence app for Confluence Server and Confluence Data Center – is “likely to be exploited in the wild" after someone “discovered and publicly disclosed the hardcoded password on Twitter.”
“A remote, unauthenticated attacker with knowledge of the hardcoded password could exploit this to log into Confluence and access any pages the confluence-users group has access to,” the company said. “It is important to remediate this vulnerability on affected systems immediately.”
The company said Confluence installations that do not actively have any versions of the app installed may still be affected. Questions for Confluence app is installed in more than 8,000 instances.
Uninstalling the Questions for Confluence app also does not remediate the vulnerability, and Atlassian provided two different ways for customers to address the issue by either disabling or removing the "disabledsystemuser" account.
The company also provided methods for companies to check whether their systems had been exploited.
Bugcrowd founder Casey Ellis said the bug is trivial to exploit, and therefore requires urgent attention.
“The vulnerability does require the Questions for Confluence app to have been installed which will limit the spread of impact here, but in general anyone who runs Confluence should assume that there's a potential problem, read the advisory (which I think Atlassian have done a great job on in helping their users simplifying the task of determining exposure), and act accordingly,” Ellis said.
Several other experts noted that hard coded passwords are problematic for a number of reasons, and Vulcan Cyber’s Mike Parkin said that now the password is out in the wild, it's guaranteed that threat actors will try and exploit it.
Digital Shadows CISO Rick Holland noted that hard-coded passwords significantly increase the likelihood of exploitation, especially when the passwords become widely shared.
“If you play soccer, hard-coded passwords are ‘own goals.’ Adversaries score enough goals alone; we don't need to put the ball in our own net,” Holland said. “Never use hard-coded passwords; take the time to set up proper authentication and minimize future risks.”
CVE-2022-26136 and CVE-2022-26137
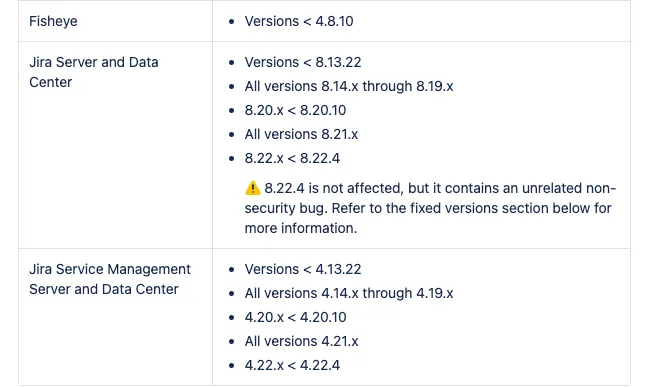
On Wednesday, Atlassian released another advisory about two other vulnerabilities – CVE-2022-26136 and CVE-2022-26137 – critical severity issues in multiple Atlassian products allowing a remote, unauthenticated attacker to bypass Servlet Filters used by first and third-party apps.
“The impact depends on which filters are used by each app, and how the filters are used. Atlassian has released updates that fix the root cause of this vulnerability but has not exhaustively enumerated all potential consequences of this vulnerability,” Atlassian said.
In a Q&A document it released alongside the advisory, Atlassian explained that the vulnerabilities affect the code included with each affected product and noted that systems are still affected even if they do not have any third-party apps installed.

For these vulnerabilities, Atlassian is unable to provide a method to confirm whether customers have been compromised and suggested users “involve the local security team or a specialist security forensics firm for further investigation.”
“Atlassian recommends checking the integrity of the application filesystem, for example, comparison of artifacts in their current state with recent backups to see if there are any unexpected differences,” the company said.
They provided specific guidance for customers using Jira, Confluence, Bamboo and Bitbucket.
Atlassian acknowledged the concerns raised by releasing multiple advisories for critical vulnerabilities back-to-back and said it plans to publish critical security advisories once a month starting this month.
They will continue to release singular advisories if a critical vulnerability is publicly and widely known and if there are verifiable reports of exploitation in the wild.
“Confluence has had no shortage of headlines,” Holland added.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.

