HPE, Extreme Networks working to address five vulnerabilities in widely used network switches
Hewlett Packard Enterprise (HPE) and Extreme Networks are in the process of fixing five vulnerabilities affecting multiple models of Aruba and Avaya network switches used by businesses, schools, hospitals, government agencies and other organizations around the world.
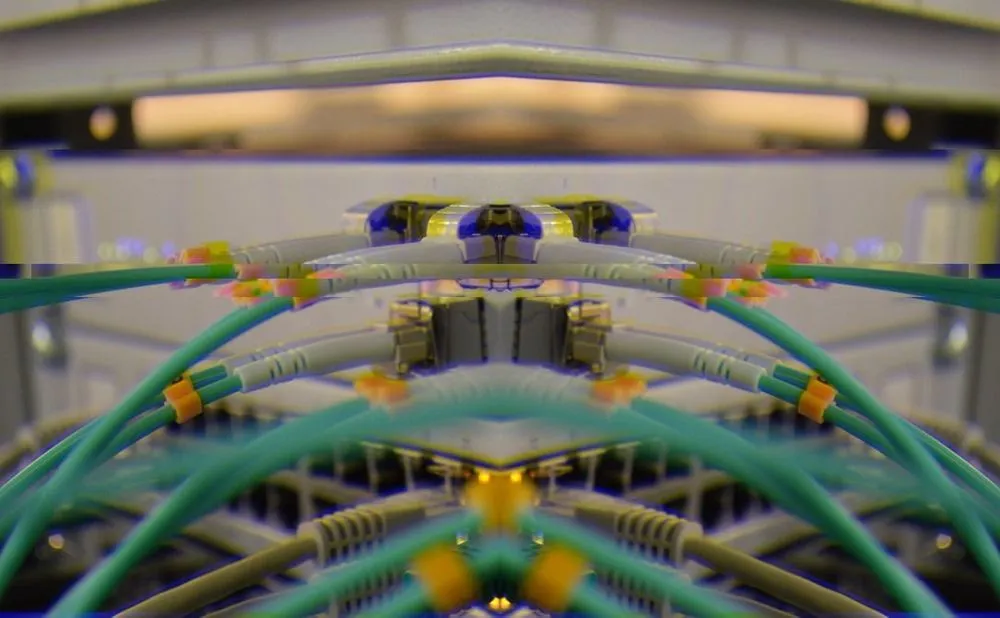
The devices are pivotal pieces of infrastructure that connect individual computers, servers, printers, cameras and other devices across networks. The bugs could allow attackers to break into multiple machines and possibly exfiltrate data, said Barak Hadad, head of research in engineering at security firm Armis.
Hadad reported Tuesday that the vulnerabilities — labeled TLStorm 2.0 as a group — stem from issues with NanoSSL, a popular library for the network security protocol known as Transport Layer Security.
“The exploitation of these remote code execution vulnerabilities can lead to breaking of network segmentation, allowing lateral movement to additional devices by changing the behavior of the switch, data exfiltration of corporate network traffic or sensitive information from the internal network to the internet [and] captive portal escape,” Hadad wrote.
Aruba is owned by Hewlett Packard Enterprise and Avaya is owned by Extreme Networks. Both companies' network switches use NanoSSL.
Avaya’s ERS3500 Series, ERS3600 Series, ERS4900 Series and ERS5900 Series are affected by the vulnerability. Aruba’s 5400R Series, 3810 Series, 2920 Series, 2930F Series, 2930M Series, 2530 Series and 2540 Series also are affected.
Extreme Networks said it has issued firmware updates addressing the vulnerabilities.
Hadad noted that there is no indication the vulnerabilities have been exploited.
HPE spokesperson Adam Bauer told The Record that HPE is aware of the issue and is “working on a firmware update to address it.”
“In the interim, we are advising customers using affected products to implement firewall controls to protect themselves,” Bauer said.
“We are not aware of any exploitation of this vulnerability involving Aruba customers.”
Armis - TLStorm 2.0 Vulnerabilities from Armis Marketing on Vimeo.
Hadad laid out two different attack scenarios. One involves using the vulnerabilities to exploit captive portals, which allow access to the internet or to the internal corporate network.
“Using the TLStorm 2.0 vulnerabilities, an attacker can abuse the captive portal and gain remote code execution over the switch with no need for authentication. Once the attacker has control over the switch, he can disable the captive portal completely and connect freely to the corporate network,” he said.
The second scenario involves using the vulnerabilities to break network segmentation, which restricts how certain users can move around. Guest users and corporate users might be limited to separate virtual local area networks, for example.
"Using the TLStorm 2.0 vulnerabilities, an attacker is able to take control of the core switch and move from the guest virtual local area network to the corporate virtual local area network,” Hadad noted.
The research shows that "network segmentation alone is no longer sufficient as a security measure,” he said.
Jonathan Greig
is a Breaking News Reporter at Recorded Future News. Jonathan has worked across the globe as a journalist since 2014. Before moving back to New York City, he worked for news outlets in South Africa, Jordan and Cambodia. He previously covered cybersecurity at ZDNet and TechRepublic.