Android malware found on Huawei's official app store
A security firm said this week it found malware on Huawei's official Android app store, the AppGallery.
Russian antivirus maker Dr.Web said it found ten apps from three developers that were infected with Joker, a type of Android malware that subscribes users to premium phone services in a tactic known as WAP fraud.
Researchers say the ten apps posed as legitimate applications, such as virtual keyboards, camera apps, app launchers, instant messengers, sticker collections, coloring programs, and games.
However, malicious code hidden in the apps operated behind the scenes to open a browser window and subscribe users to premium phone numbers, allowing the malware's operators to earn commissions.
In addition, the malware also intercepted SMS messages and push notifications in order to prevent alerting the user to their presence on the device.
Huawei removed the apps from its store, but not devices
After receiving an alert from Doctor Web, Huawei hid the trojans in the AppGallery store to protect users. The company will conduct an additional investigation to minimize the risks of such apps appearing in the future.Huawei spokesperson
But while the apps listings were hidden on Huawei's app store, they are still present on user devices and are putting users at risk. According to Dr.Web, around 500,000 Huawei users downloaded the apps.
Huawei smartphone owners who want to remove the apps will need to go into their operating system's Apps section and search for one of the ten app names below. In case they find any of the apps listed underneath, users are also advised to alert their mobile operator about unwanted surcharges on their next months' bills.
Super Keyboard (com.nova.superkeyboard)Happy Colour (com.colour.syuhgbvcff)Fun Color (com.funcolor.toucheffects)New 2021 Keyboard (com.newyear.onekeyboard)Camera MX - Photo Video Camera (com.sdkfj.uhbnji.dsfeff)BeautyPlus Camera (com.beautyplus.excetwa.camera)Color RollingIcon (com.hwcolor.jinbao.rollingicon)Funney Meme Emoji (com.meme.rouijhhkl)Happy Tapping (com.tap.tap.duedd)All-in-One Messenger (com.messenger.sjdoifo)
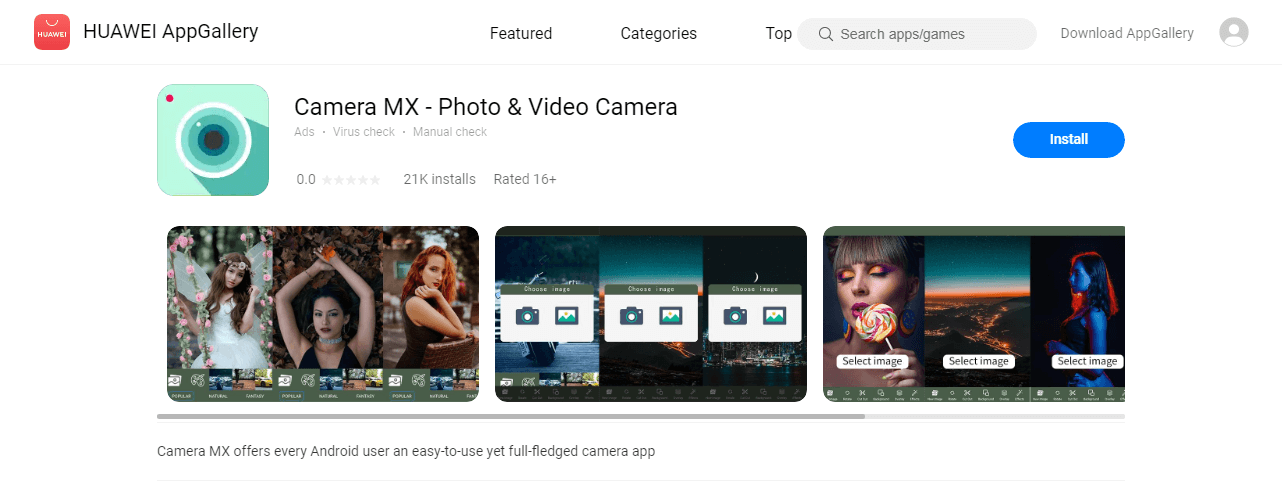
Image: Dr.Web
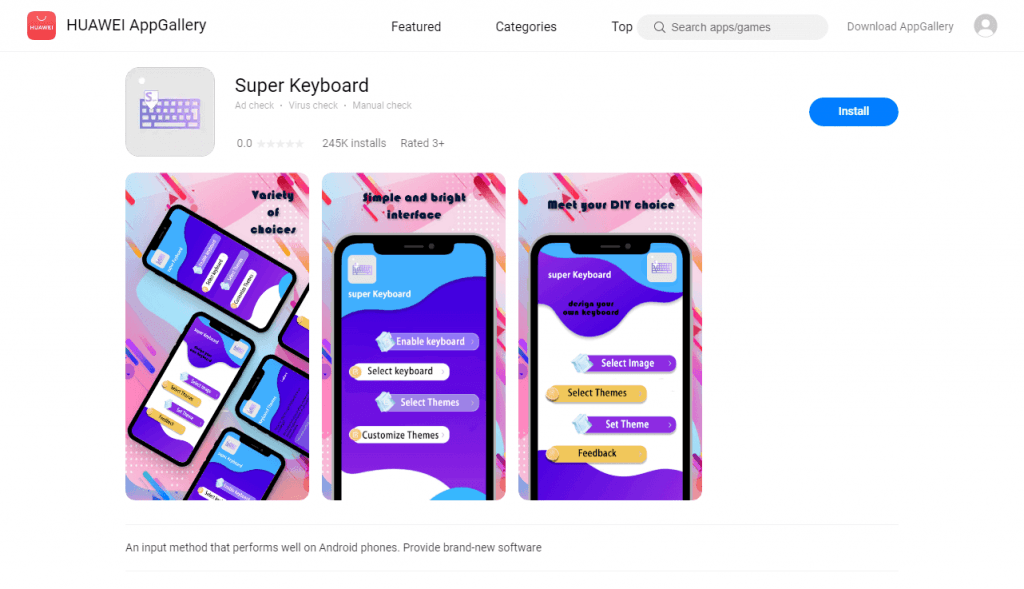
Image: Dr.Web
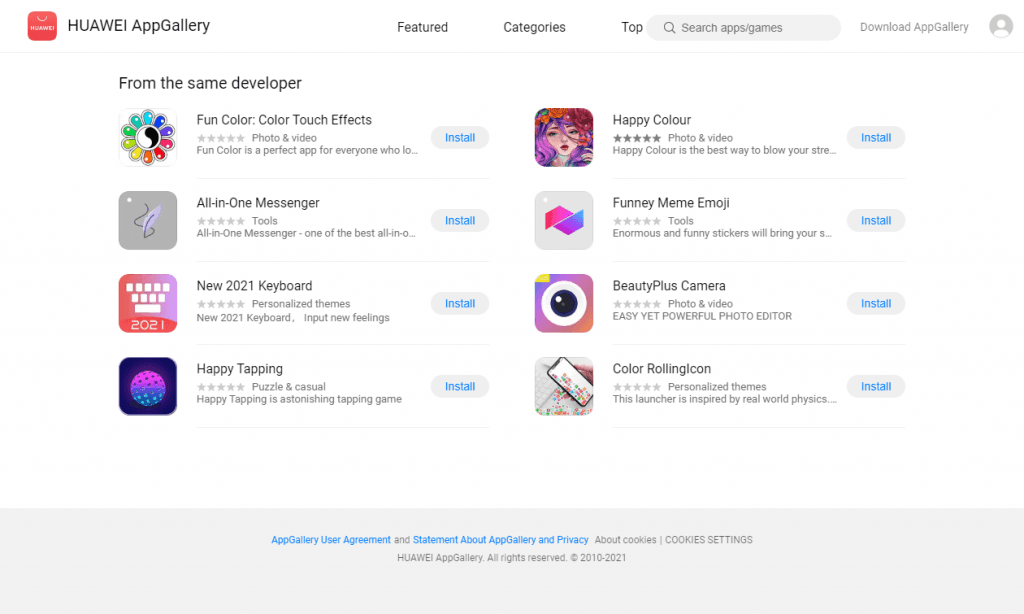
Image: Dr.Web
In addition, Dr.Web researchers said they also found versions of the same Android apps on the official Google Play Store as well. A list of these apps is available on the security firm's GitHub repository, but a cursory search performed by The Record found that the apps have already been removed from the Play Store.
One of the Play Store's biggest scourges
But news that the Joker malware has reached Huawei's official store is not a surprise for anyone who's been tracking the Android malware ecosystem.
The Joker malware, which has been operating since 2017, has made a habit of slipping malicious apps on the Play Store over the years [1, 2, 3, 4, 5, 6, 7, 8, 9, and more].
In a January 2020 blog post, Google, which tracks the Joker malware under the codename of Bread, said it blocked or removed more than 1,700 apps submitted to the Play Store over the past three years that contained versions of the Bread malware.
This statement says more than some people might realize. If a company like Google —which has invested considerable financial and software resources into its Play Store security— was not able to detect or stop the Joker gang, other smaller app stores like Huawei's AppGallery stand no chance.
The Record has reached out to Huawei with additional questions in regards to its app store defenses, and its ability to detect Joker and other malware when apps are uploaded on the store, rather than after the malware has already infected users.
While Dr.Web said this was the first time they found malware on Huawei's AppGallery, a study published in February 2020 listed Huawei's app store as one of the top 5 malware-laced app stores on the internet.
Catalin Cimpanu
is a cybersecurity reporter who previously worked at ZDNet and Bleeping Computer, where he became a well-known name in the industry for his constant scoops on new vulnerabilities, cyberattacks, and law enforcement actions against hackers.



