Android apps caught stealing Facebook credentials
Security researchers from Russian antivirus maker Dr.Web have discovered nine Android applications hosted on the official Google Play Store that contained functionality to steal Facebook account credentials.
In a report last week, the security firm said it reported the apps to Google, which removed them from the store after confirming the malicious behavior.
According to the security firm's investigation, the apps had been downloaded more than 5.8 million times before being yanked offline.
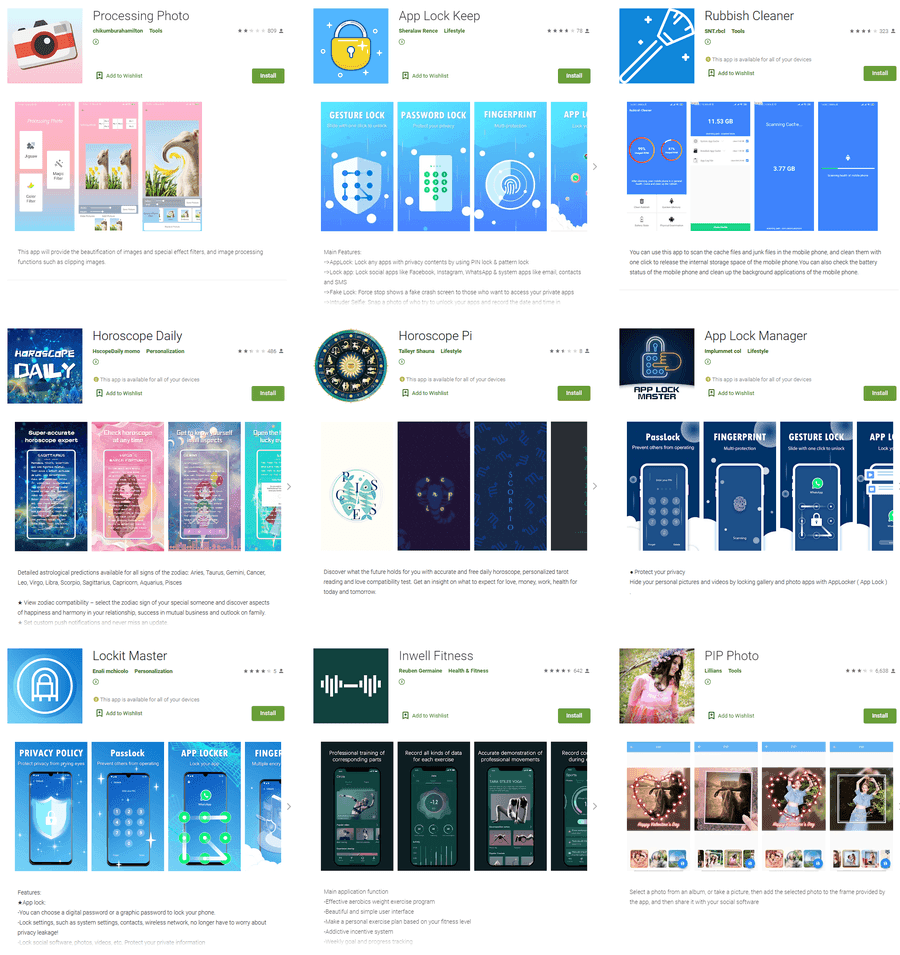
| App name | Developer name | Download count |
|---|---|---|
| Processing Photo | chikumburahamilton | 500,000 |
| App Lock Keep | Sheralaw Rence | 50,000 |
| App Lock Manager | Implummet col | 10 |
| Lockit Master | Enali mchicolo | 5,000 |
| Rubbish Cleaner | SNT.rbcl | 100,000 |
| Horoscope Daily | HscopeDaily momo | 100,000 |
| Horoscope Pi | Talleyr Shauna | 1,000 |
| Inwell Fitness | Reuben Germaine | 100,000 |
| PIP Photo | Lillians | 5,000,000 |
While similar incidents have happened before, Dr.Web said these nine apps stood out because of the novel method they used to collect Facebook credentials.
While most apps try to show a fake Facebook login screen on top of the legitimate Facebook app, these nine actually used Facebook's legitimate login page, as detailed before:
- All apps contained legitimate functionality but with a heavy dose of ads.
- Users were told that they could remove ads by connecting their Facebook account.
- Users who chose to do so were redirected to the real Facebook login page, loaded inside a WebView minimal browser component.
- Since the malware was control of the WebView component, the attackers also loaded malicious code that siphoned the user's login credentials right from the legitimate Facebook login page.
Users who think they downloaded any of the apps listed above are advised to change their account credentials as soon as possible, as their accounts could be abused to send spam or run illicit advertising campaigns on Facebook, a tactic for which Facebook sued four Vietnamese Android app developers last week.
Catalin Cimpanu
is a cybersecurity reporter who previously worked at ZDNet and Bleeping Computer, where he became a well-known name in the industry for his constant scoops on new vulnerabilities, cyberattacks, and law enforcement actions against hackers.



