An Interview With Ares, a Russian Coder Who Built a Swiss Army Knife for Hackers
Editor’s Note: In 2012, a Russian hacker who went by the moniker Ares received a routine email asking about Intercepter-NG, a popular tool he developed that can be used for traffic interception.
The user was having difficulty—the tool would crash when he tried using it to parse large amounts of data—and Ares was quick to reply. “Man, you patch quick!” the user wrote in response.
According to Ares, the messages came from [email protected], the email address used by NSA contractor Edward Snowden. About a year after their first conversation, Snowden would be living as a fugitive, wanted by the U.S. government for revealing thousands of classified documents to journalists.
Ares talked with Recorded Future expert threat intelligence analyst Dmitry Smilyanets about Intercepter-NG, his correspondence with Snowden, and other topics in a recent interview. The conversation was conducted in Russian, and was translated to English with the help of a professional translator. The interview below has been lightly edited for length and clarity.
Dmitry Smilyanets: Tell me about Intercepter-NG—why did you create it and how do you see its development in the future?
Ares: Intercepter-NG is a sniffer, network packet analyzer, a tool for carrying out network man-in-the-middle attacks. It also includes many other functionalities, such as network brute-force attacks and file recovery from traffic. Imagine that you combined Cain & Abel, Wireshark, Network Miner, THC-Hydra, and a number of other separate utilities with each other, and you will get Intercepter-NG. Among other things, it also has unique network attacks that, in principle, are not found in any other tool. This year the project turns 15 years old.
In the mid-2000s, there were very few interesting networking tools for Windows, I wanted to make one, and most importantly, make it free. I have ideas for the future. Maybe I will convert it to a cross-platform open-source project, maybe something else…
DS: How is your product being used?
Ares: The range of applications of Intercepter-NG is very wide. As I have already said, it has a very diverse functionality, but despite the seeming simplicity and abundance of graphical controls, very specific technical training is required from the user. Among the users are system administrators, information security specialists, penetration testers, but, unfortunately, it can also be used by people with malicious intent.
Blue Teams members can use Intercepter-NG in some sense as a honey pot, tracking attempts to connect to various services or attempts to brute force passwords. Red Team members can directly carry out offensive actions on the network: intercepting traffic, gaining remote access, and so on.
DS: Tell us in detail about your communication with Edward Snowden.
Ares: In mid-2012, one of the English-speaking users of my program wrote to me and said that under certain conditions the program crashes. I made the necessary changes and fixed the flaw. This was followed by a series of newly revealed mistakes on his part.
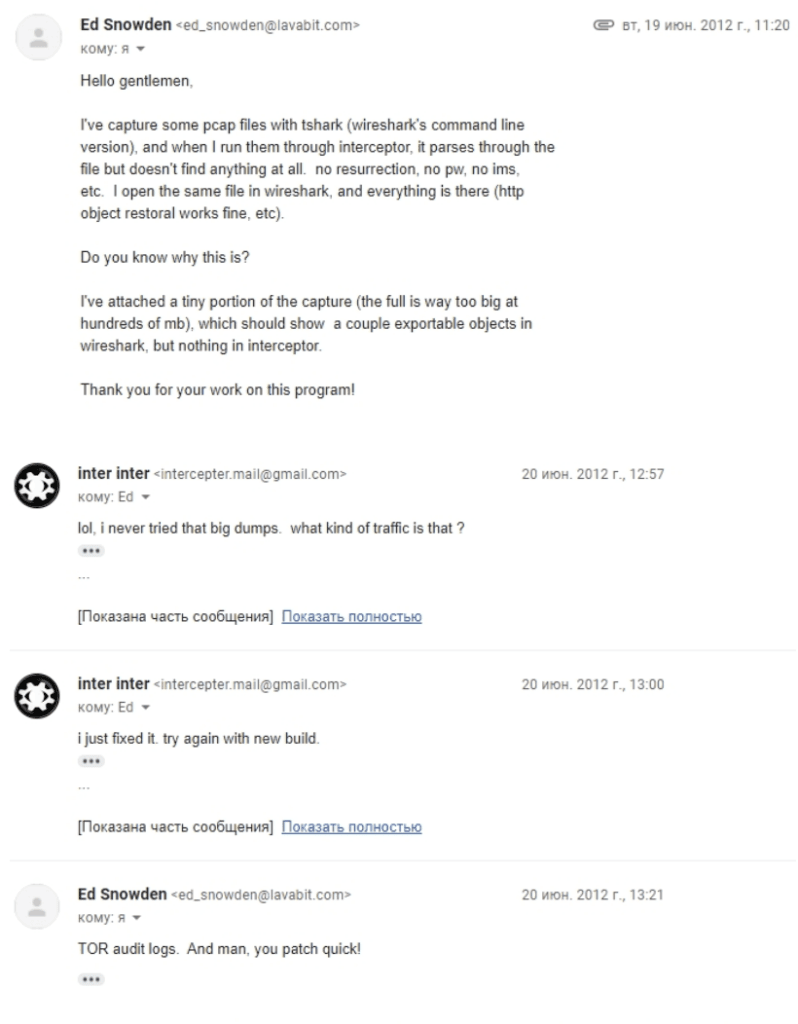
As a rule, crashes took place with large amounts of data—gigabytes and tens of gigabytes. I asked where this traffic came from, to which my interlocutor replied that it was from the output node of the Tor network. To solve some of the software errors, I needed to get a part of the data on which the program crashed. Thus, I had at my disposal a certain amount of pcap files with which I was able to improve the performance of my application [editor’s note: Tor is an anonymity network that keeps a user’s identity private by encrypting traffic and relaying it across waypoints to make it difficult to trace. Packet capture, or pcap, files are created by network analyzers to collect and record packet data from a network]. After a while, the conversation stopped, but on May 30, 2013, I wrote him a message with a request to provide some files with traffic, because I was preparing for the release of a new version of Intercepter-NG and wanted to test new protocol handlers, but there was no reply, and I forgot about this conversation. Only six months later, when I was flipping through the old correspondence, I noticed the name of my interlocutor—[email protected]. That was a surprise!
DS: Do you think he uses your product today?
Ares: How should I know? Our correspondence ended in 2012... I will take this opportunity to say hello to him!
DS: What do you think about his actions and about him as a professional?
Ares: He is definitely a great technical specialist, not some ordinary system administrator. I think everyone knows his position, my assessment of his actions does not matter.
DS: You started a YouTube channel and put out a few interesting videos and interviews, but you don't reveal yourself. Why?
Ares: First of all, it's a habit. We are supposedly hackers, we must hide and remain anonymous, although there is nothing special to hide. Secondly, once upon a time, I was invited to participate in a podcast, and then I changed my voice. The result is such a mysterious persona, to which a mask has now been added. It's so cool. I think it is quite obvious that after the launch of the YouTube channel, the coming out from the shadows is not too far away.

My main activity is not related to IT, my project and current media activity are more of a hobby. In addition, I am engaged in scientific and semi-scientific research. That's all I can say.
DS: How has the hacking scene changed over the past 20 years?
Ares: In my opinion, it has not only changed but died—forever. For me, the hacking scene existed from the late 1990s to the late 2000s. It was a time when the best hackers, programmers, crackers, and virus writers united in groups and exchanged information, interacted with each other and lived by it. In every country there were central scenes, and these people hung out mainly on IRC. The golden age was the early 2000s when groups like TESO, uNf, THC, w00w00, 29a, ADM, Phenoelit, and others were spoken about. It was a boom in the development of many vulnerability exploitation techniques, and a large number of RCE vulnerabilities were found in the most popular software products. After that, new protection mechanisms began to be actively developed. Many members of the hacker community started creating their own information security companies or got jobs for IT giants. Someone decided to engage in illegal activities... Therefore, people dispersed, these groups started releasing fewer and fewer tools. Intercepter-NG, by the way, at first was positioned exactly as a release from a hacking group in which I was a programmer.
DS: What do you think about ransomware? Which variant do you think is the most technically advanced and why?
Ares: From a technical point of view, a crypto locker ransomware is a very primitive type of malware, even a schoolchild could write it, which is why the very first crypto lockers were so poor that virus analysts constantly found errors in them, thanks to which it was possible to recover encrypted data. It is clear that experienced malware coders began to use asymmetric encryption, in which the ability to independently decrypt data trends to practically zero. From an ethical point of view, I strongly dislike crypto lockers and condemn people who use them for blackmail and extortion.
DS: What advice would you give to companies that have not yet been attacked by ransomware? How can they protect their corporate network from attacks?
Ares: Unfortunately, the human factor is almost always the weakest link. You have to work with the personnel and exclude situations when an ordinary employee executes files of unknown origin and content. Critical data should be backed up regularly. All this is pretty obvious.
DS: You previously taught young information security specialists. Do you think Russia is able to provide jobs for graduates in 2021? Or will they need to continue to find illegal opportunities??
Ares: Taught young specialists—that’s overstating it. I once gave a lecture for students at one university, nothing more. With regard to work... I do not think that the state should be obligated to allocate jobs for newly graduated specialists. Are there vacancies for young IT specialists in government structures? I am sure there are. Should tomorrow's graduates have to arrange their lives on their own? They should. If you are not hired anywhere, then you probably did not study well and you are not much of a specialist. This is capitalism.
DS: What do you think about the attribution of the SolarWinds attack?
Ares: I don't follow those types of hacks, I'm not interested. Regarding accusations against Russian hackers in all sins—this is an established tradition. We have American presidents pissing in hallways, and they see hackers in earflaps everywhere.
DS: Tell me a secret.
Ares: “I'm Batman. Your secret is safe.”
Dmitry Smilyanets
Mission-driven and Russian-speaking intelligence analyst with type A personality. Dmitry has twenty years of experience and expertise in cybercrime activity that includes being a former member of an elite Russian-based hacking organization.


