Adult cam site StripChat exposes the data of millions of users and cam models
StripChat, one of the internet's top 5 adult cam sites, has suffered a security breach and has leaked the personal data of millions of users and adult models.
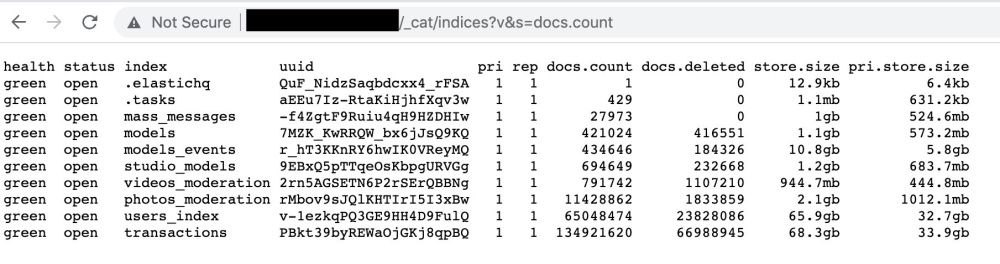
The leak, discovered by security researcher Bob Diachenko, took place earlier this month after StripChat exposed its ElasticSearch database cluster on the internet without a password for more than three days between November 4 and November 7.
Diachenko, who documented his findings in a blog post published today, said the exposed servers leaked a treasure trove of highly-sensitive information, such as:
- Data of 65 million users registered on the site (username, email, IP address, ISP details, tip balance, account creation date, last login date, account status)
- Data of 421,000 models broadcasting on the site (username, gender, studio ID, live status, tip menus/prices, strip score)
- Data of 134 million transactions (information about tokens and tips paid by users to models, including private tips)
- Data about 719,000 chat messages saved in a moderation database (the user and model ID involved in the conversations)
Possible GDPR violation from StripChat's part
Diachenko said he notified StripChat about the leaky cluster as soon as he spotted the servers and determined that the data belonged to the company.
The researcher said the cam site secured its server a few days later, but without providing a reply or explanation for what happened.
Despite suffering a major security breach that has impacted the personal information of more than 65 million users, at the time of writing, StripChat has yet to publicly disclose or acknowledge the incident, an action that may incur a severe GDPR fine for the Cyprus-based company.
StripChat has not returned requests for comment sent by The Record via email and their Twitter account earlier today.
It is unclear if someone else besides Diachenko has discovered and accessed StripChat's database, but if they did, this data would put all those involved at serious risks.
"The exposure could be a digital and physical threat for both Stripchat viewers and models. IP addresses, which can be used to approximate someone's location, are particularly worrying. They could enable someone to find and stalk, harass, or even assault someone in the database," Diachenko said today.
"Aside from physical violence, the identifying information could be used to extort, bully, or humiliate victims who thought their online activities were private," the researcher added.
Third major cam site to suffer a breach
The StripChat incident marks the third major security breach at an adult cam site operator after Cam4 exposed 7 TB of internal data in May 2020, and PushyCash exposed the details of 4,000 cam models in January 2021.
In August 2019, Diachenko also found a similarly highly-sensitive data leak at a Spanish brothel chain running "men's clubs" in Barcelona and Valencia, where prostitution is legal, but not in an organized manner such as brothel houses, which are still considered illegal.
Update: In a blog post, StripChat confirmed the incident and blamed it on an error during a routine reconfiguration of their servers. It said that passwords, payment details, and account verification documents were not accessed in the breach.
Catalin Cimpanu
is a cybersecurity reporter who previously worked at ZDNet and Bleeping Computer, where he became a well-known name in the industry for his constant scoops on new vulnerabilities, cyberattacks, and law enforcement actions against hackers.