10,000+ unpatched home alarm systems can be deactivated remotely
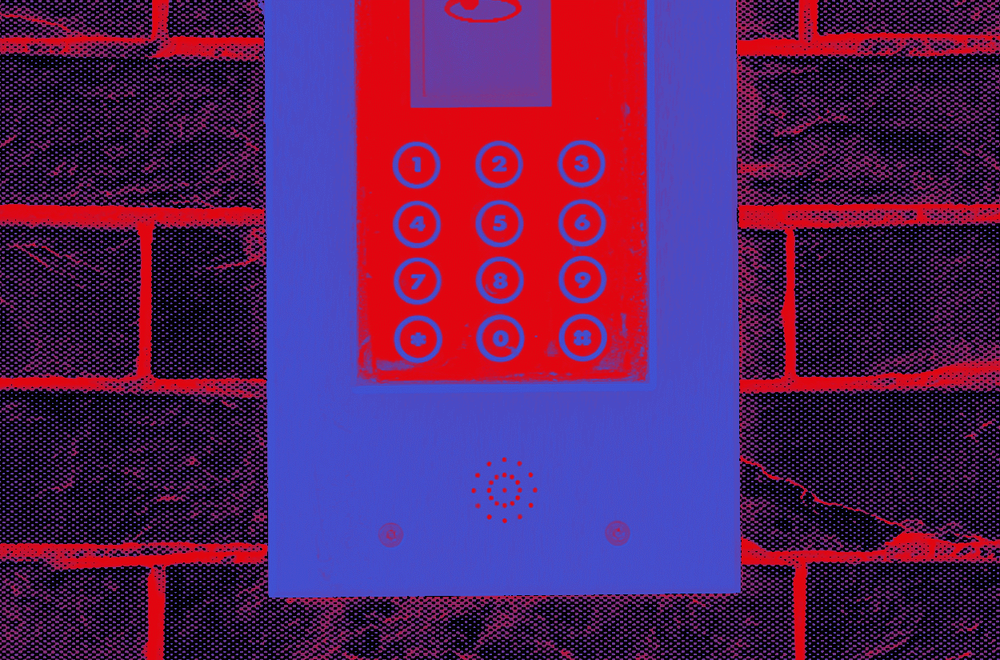
Thousands of ABUS Secvest smart alarm systems are currently unpatched and vulnerable to a bug that would allow miscreants to remotely disable alarm systems and expose homes and corporate headquarters to intrusions and thefts.
ABUS patched the bug in January, but three months later, more than 90% of its customers have yet to apply the firmware patch.
Dutch security firm EYE, which discovered and reported the issue to ABUS last October, estimated the total number of Secvest alarm systems connected online to around 11,000, based on internet scan data collected by security firm Rapid7.
Most systems are located in Germany
In a blog post published on Tuesday, three months after ABUS released the Secvest patch, EYE security researcher Niels Teusink said that only around 1,000 of the 11,000 internet-connected Secvest alarm systems were running the latest firmware versions, meaning that roughly 10,000 alarm systems were still exposed to attacks.
According to Teusink, most of these systems are located in Germany, with a few hundred other systems spread across German-speaking countries like Austria and Switzerland, but also the Benelux.
| Country | Count |
|---|---|
| Germany | 10.184 |
| Switzerland | 445 |
| Austria | 426 |
| Netherlands | 376 |
| Luxembourg | 89 |
| France | 37 |
| Belgium | 35 |
| Other | 87 |
| Total | 11.679 |
As for the bug, Teusink said the vulnerability resides in the alarm system's web administration panel, which customers can use via a browser or mobile app to control the Secvest systems.
"What I found is that although the HTTPS request to deactivate the system requires authentication, many other requests do not," Teusink said.
One example, Teusink explained, was that attackers could send a specific web request to a remote internet-connected Secvest alarm and tell it to start its siren, which would emit a loud sound in people's homes and workspaces.
With some clever scripting, this process could be automated for a prank that would trigger security alarms at thousands of locations across Germany and western Europe.
But while the alarm couldn't be deactivated with one single request, Teusink said the attacker could use the same bug to access and download the alarm system's configuration file, which would trigger other issues.
Since this file also contained the usernames and passwords of all users registered on the alarm system, Teusink said the attacker had all they needed to connect to the alarm system with valid credentials and then disable it at a specific location.
Bugs could be used in real-world intrusions
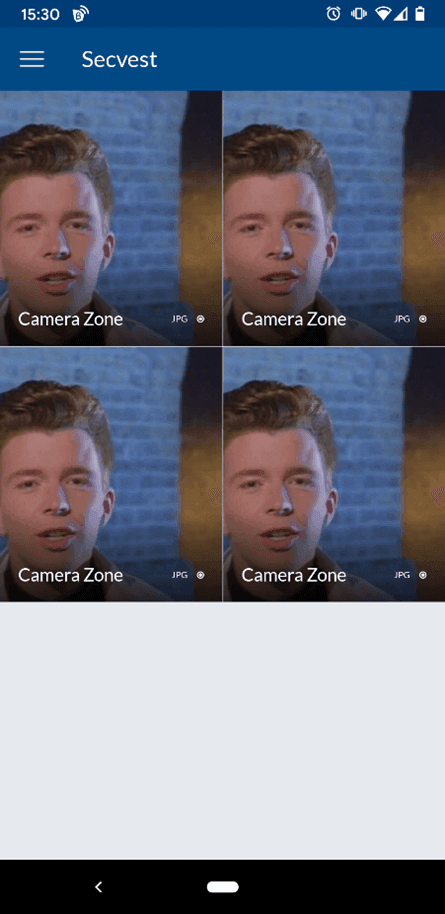
In addition, the EYE security researcher said that the information from this configuration file, such as the alarm system name, IP address, access to raw camera feeds, and more, could be used by an attacker to determine the physical location of an alarm system.
This way, hackers working with criminal groups could abuse the bugs to orchestrate intrusions at high-value properties.
Moreover, Teusink said it was also possible to disable or tamper with security camera feeds and prevent the intruders from being captured on video footage during an intrusion after the alarm was disabled.
All the issues above should be enough for any Secvest system owner to apply updates. However, things aren't that simple. Teusink said that applying the firmware update requires special "installer" permissions, which in many cases the alarm owners might not possess if the alarm was installed by a third-party company—a possible reason why the patching rate has been so abysmal.
ABUS did not return a formal request for comment sent earlier this week.
Catalin Cimpanu
is a cybersecurity reporter who previously worked at ZDNet and Bleeping Computer, where he became a well-known name in the industry for his constant scoops on new vulnerabilities, cyberattacks, and law enforcement actions against hackers.